The First-timer’s Guide To Hack-proof WordPress Security
One-fourth of the Internet runs on WordPress! Let that sink in.
If you have forty websites in a day, at least ten of them would be hosted on WordPress. User-friendliness, a massive library of themes, plugins, extensions and continuously improved security makes WordPress a favorite web hosting platform.
Its popularity also makes WordPress the most targeted CMS platform in the world. More than 70% of top ranking websites hosted on WordPress displayed serious security vulnerabilities. Well, your website could also be one among them if you are not strong on the security front.
Here is a quick guide to WordPress security. The things you ought to know and do to keep your WordPress website from succumbing to an attack.
To begin with, let us look at some of the most common methods how WordPress websites are attacked:
-
SQL Injection – injecting malicious codes and statements into the website’s URL where user information is gathered
-
File upload – uploading malicious codes to the website’s server that disrupts its smooth functioning
-
Brute Force attacks – Repeatedly trying various usernames and passwords to make a forced entry into the website
-
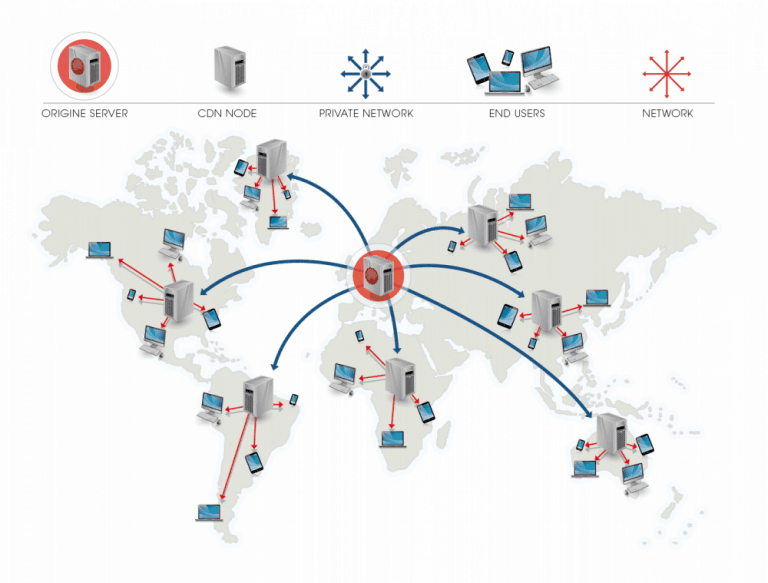
DDoS – Distributed Denial of Service caused due to bots-led heavy traffic
-
Phishing – Stealing the credentials of individuals by posing as a trusted site or person
-
Remote Code Execution (RCE) – A hacker executes arbitrary code on the website through remote access
Well, there are still more WordPress security vulnerabilities. These are the common ways how WordPress sites are targeted by hackers.
Now, let’s see some basic steps how you reinforce security for your WordPress website.
Just like protecting your computer with an antivirus software, it is necessary to protect your WordPress website too. The tools and the methods to use them differs slightly. Some basic things you can do include:
-
Protecting your admin dashboard with a strong password
-
Changing the default path of the admin directory
-
Setting up a firewall that can monitor incoming and outgoing traffic
-
Configuring a strong WordPress security plugin
-
Using File Transfer Protocol Secure (FTPS) instead of FTP
-
Securing FTP credentials with trustworthy users
-
Updating WordPress every time a security patch is available
-
Scheduling and taking regular backups
Securing your admin panel
To prevent DDoS and brute force attacks take place on WordPress website, it requires to enable HTTPS request for WordPress admin panel. You have to buy SSL certificate from trusted Certificate Authorities like Comodo and install it on your web server to secure admin panel. This admin panel page is located in the root directory of your WordPress site, which is easy for a search engine bot to crawl. You can edit or even take control page using a robots.txt file. After configuration of SSL certificate, your WordPress site must accessible over https.
Just like the admin panel, even your wp-config.php file contains critical information like your website’s database connection information and so on. Relocating it to some new folder or subfolder would help keep the hacker getting access to key information that would complete the hacking process.
Similarly, changing the wp_ prefix for your database directory would also have the safe effect. The database’s location could not be traced by the hacker unless
Next, Disable Plugin and Theme Editor
Worst case scenario, let’s assume your website is hacked. This gives the hackers access to your plugin and theme editor. It is literally giving the hacker access to your website’s frontend and its overall functioning.
While some hackers might argue that a hacker finding his way into the admin dashboard itself is fatal, disabling the plugin or theme editor still has some chance of survival. You can disable the editor by accessing the settings under Appearance -> Editor and Plugins -> Editor.
Set up some rules for your .htaccess File
The .htaccess File is often used to override web server settings in order to optimize performance. While it is a productivity tool in the hands of a developer, for a hacker it is a deadly weapon to destroy the website once and for all.
The uniqueness of the file is that it cannot be seen ordinarily while you are browsing directories. You have to go to cPanel -> Files > File Manager in order to access the file and make any changes. It is recommended that you set up some rules like who can access this file, who can edit it, and whether no other user other than the admin is allowed to access it. It is like deciding who holds the key to your home when you are locking out.
Change default presets
WordPress comes with some default presets like the “admin” username. A generic username combined with a weak password is more than enough to allow the hacker to find his way into your website. To make things easier for hackers, WordPress returns a message if you have entered the wrong username or the password.
So, changing your default preset as the admin username to something more secure and hack-proof is a sensible thing to do.
Hide the login page
If your website does not require users to sign in or create accounts, it would be a great thing to hide the login page altogether. This would prevent the hacker from trying any brute force attacks on your page.
You can also limit the number of failed login attempts a user can have before locking out the login attempts for the session or the day, like in banking websites.
If you don’t have an option but to have a login page, it is recommended that you hide the WordPress version number. Even that tiny information can be used by a hacker to spot vulnerabilities and exploit them straight away.
Endnote
As an end note, here are some WordPress security best practices that can take care of your WordPress website security:
-
Configure an SSL certificate, like a Comodo SSL Certificate
-
Run regular vulnerability assessments
-
Relocate your .httaccess file
-
Change default presets
-
Review abnormal log changes
-
Do a thorough security audit to spot loopholes
These steps should help prevent a large proportion of the attacks on your WordPress website.