How to Set Up & Use VPN?

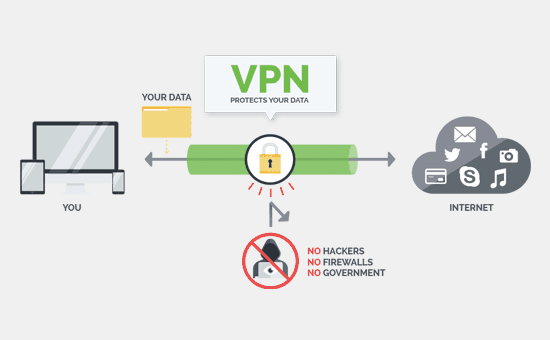
Virtual private networks (VPNs) give PC clients an extensive variety of capacities and advantages. First off, VPNs enable you to safely associate with remote networks through the web, allow secure associations of numerous networks, and help support your online security and protection.
Everybody ought to utilize a virtual private network or VPN, regardless of whether you’re associating with the Internet on your PC or your cell phone. That may sound jumpy, yet there are genuine dangers out there, and they’re just deteriorating. On Wi-Fi networks, corrupt people can endeavor to block your data. hope this would clear your doubt regarding what is vpn?

Furthermore, at whatever point you interface with the web, your Internet Service Provider (ISP) approaches all that you send and has been given the green light from Congress to offer your anonymized data to publicists, as well. Out on the totally open web, publicists and spies can track your developments amongst sites and observe your area by looking at your IP address.
It’s startling out there.
The truth of the matter is the web was not intended to secure your protection. It was made for simple data trade, not client security, anonymization, or scrambled correspondence. While HTTPS goes far toward securing your data, it doesn’t make preparations for ISP snooping or nearby network assaults—a noteworthy issue in the event that you ever utilize an association that isn’t yours, for example, one at an inn or a coffeehouse.
There are different strategies for setting up a VPN, however the most straightforward is to the apparatuses given by your working arrangement of decision. In any case, observe:
You may need to counsel your VPN supplier for particular settings, and you’ll have to know your username and password to validate. Also, you’ll need to rehash these directions for each new server you associate with, while your outsider VPN customer will make this less demanding. The vast majority will simply have a couple of servers, yet businessmen could possibly invest a lot of energy working out a powerful rundown of servers.
Uses Of VPN:
Similarly as with any security device, it’s essential to comprehend the confinements of a VPN. All things considered, you wouldn’t anticipate that a kevlar vest will spare you from dropping out of a plane or a parachute to stop a slug.
When you switch on a VPN, your movement is directed through an encoded passage to a server worked by the VPN organization. That implies that your ISP and anything (or anybody) associated with your switch won’t have the capacity to see your web activity. From the VPN server, your activity exits onto the general population web. Except if you’re made a beeline for a site that utilizations HTTPS, your activity is never again encoded.
Since your movement seems to originate from the VPN’s server, your genuine IP address is adequately covered up. That is essential, since IP addresses are appropriated topographically and can be utilized to gather somebody’s area. On the off chance that somebody checks your IP address, they’ll see the IP address of the VPN server. This can prove to be useful in the event that you need to parody your area. By interfacing with a VPN server in London, you can influence it to show up as though you are getting to the web from the UK.
Working:
Also, sites can track your developments through treats, program fingerprinting, online trackers, and other dubious apparatuses. Utilizing a promotion blocker, for example, Privacy Badger stifles these ever attentive nasties and can make it considerably harder for publicists to take after your developments over the web.
At long last, since you have a VPN doesn’t mean you can disregard the security nuts and bolts. While some VPN administrations guarantee they can square malware, we prescribe independent antivirus programming for your PC, in light of the fact that these apparatuses are planned particularly to shield your PC from pernicious programming. You ought to likewise utilize a secret key administrator, on the grounds that reused passwords are a noteworthy purpose of disappointment. Another safety measure is to utilize presence of mind while tapping on connections or opening email connections. Phishing assaults—when an aggressor utilizes a fake site that imitates a well-known one to deceive you into entering your login certifications—are so basic as to nearly be ordinary, so remain caution.
Choosing Right service:
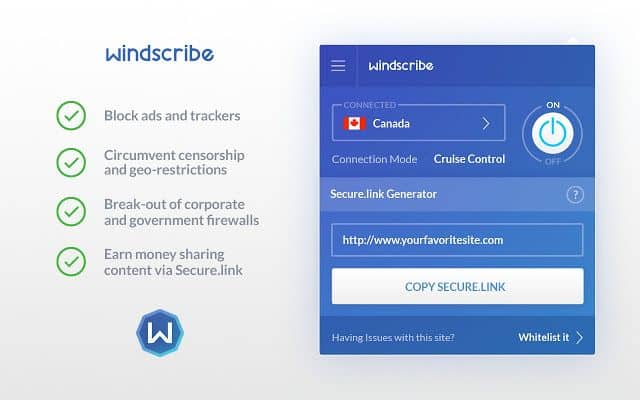
There are numerous of VPN’s providers flooding over the internet. You can choose wisely according to your needs & pricing. But I will recommend using best free VPN like windscribe, Tunnel Bear or VPN application optimized for mobile devices.
Before you join with a VPN, make certain to peruse its terms of administration. This record will layout what data the VPN gathers and what it does with that data. Most organizations say that they don’t log activity, which is extraordinary. Others go further, saying that they don’t screen client action by any stretch of the imagination. This is vital, on the grounds that a VPN approaches all the data you’re endeavoring to shield from others. The best terms of administration make every one of these issues obvious, while the most exceedingly bad are hazy on the points of interest and written in legalese. On the off chance that understanding one of these records feels like you’re endeavoring to decipher the Dead Sea Scrolls, think about attempting another administration. TunnelBear, for instance, plainly plots its task in straightforward dialect.
It’s additionally helpful to see where the VPN organization is based. Remember this isn’t generally the physical area of the business, however a legitimate refinement that diagrams what locale the organization works under. NordVPN, for instance, is in Panama, while ProtonVPN is in Switzerland. That implies that these organizations are not indebted to information maintenance laws, which would expect them to clutch certain data that could be gotten by law requirement.
VPN is based on trust, confidentiality and usage access. You can change them when it fails to do so.

Setup & Getting Started:
Once you’ve settled on a service, next thing is setting it up. To do it, download the company’s app. There’s usually a downloads page for this on the VPN service’s website. Go ahead and download the apps for your mobile devices as well; you’ll want to protect as many of your devices as you can. Generally, you pay one subscription fee for a certain number of licenses (usually five) and then you can use the service on any device for which it provides apps.
Once you’ve installed the apps, you’re prompted to enter your login information. In most cases, this is the username and password you created when you signed up for the service. Some companies, such as Private Internet Access assign you a username that’s different from your billing credentials, in order to provide customers with more privacy.Once you’re logged in, your VPN app usually connects to the VPN server closest to your current location. That’s done to provide better speeds with a VPN, as latency and speed reductions increase the farther the VPN server is from your actual location. That’s it: Your information is now being securely tunneled to the VPN server.Note that you do not have to install the VPN company’s app. Instead, you can configure your device’s network settings to connect directly to the VPN service. If you’re concerned about the potential for surveillance within app ecosystems, this might be a good option for you. Most VPN services will have documentation on how to configure your device.
Tune & Optimize
Getting your VPN set up and working at an essential level isn’t the finish of the story. Set aside the opportunity to look at the customer settings and ensure they suit your requirements. Begin with the default convention. This ought to be OpenVPN UDP for ideal speed and security (OpenVPN TCP is slower, PPTP specifically is less secure). Check any startup alternatives. On the off chance that you require insurance constantly, you may have the capacity to set the customer to begin with Windows and naturally interface. However, in the event that you just utilize the VPN sporadically, you could free up a couple of assets by just propelling the customer when required.
Numerous VPN customers have top choices frameworks where you can feature normally utilized servers for simple access later. On the off chance that your customer underpins this, try it out and it could make your life somewhat less complex.
Peruse some other settings on offer, and check the VPN bolster site for clarifications of what they’re for. Customer default settings aren’t in every case sensibly picked, and you may well discover fascinating highlights you didn’t know existed.
Troubleshoot
A VPN supplier’s own particular customer as a rule works immediately, yet in the event that you’re not all that fortunate, and your supplier’s help site doesn’t help, there a couple of things you can attempt. Shut down and restart the customer. Reboot your gadget if that doesn’t have any effect. In the event that you have some other VPN programming running, ensure you’re disengaged, at that point shut it down.
VPN customers depend on their driver being set up accurately. A few customers have a Repair work which viably reinstalls the driver – check any menus or Settings screens to check whether there’s a comparable alternative accessible.
In case you’re getting a confirmation or login issue, check your accreditations. VPNs handle these in various ways – many enable you to make them, others produce logins for your benefit, some give you isolate qualifications for consistent and OpenVPN logins – and it very well may be anything but difficult to get stirred up. Re-read any appreciated email or amateur’s guide the VPN may have sent you when you joined.
Some of best & renowned VPN are listed below:
Tunnel Bear
NordVPN
Windscribe
Hideme
ProtonVPN
Conclusion:
VPN are made to help in increase of our privacy & help in data protection from unwanted uses. An excessive number of you aren’t utilizing a VPN, and possibly that is on the grounds that they appear as though arcane security apparatuses. In any case, numerous organizations have endeavored to make them well disposed and simple to utilize. Most are currently set-and-overlook security devices, as it ought to be. Also, however opening your wallet to prepare for potential dangers is continually irritating, purchasing a VPN is truly outstanding and most effortless approaches to watch your web activity from, well, pretty much everybody.





i have been using ivacy for a few months. works perfectly on all my devices.
Thank you for your comment
I use purevpn and its easy to connect. Works fine on apps too.